
The researchers added: “This marketing campaign is notable in that it demonstrates how impactful smishing operations may be executed utilizing easy, accessible infrastructure. Given the strategic utility of such gear, it’s extremely possible that comparable gadgets are already being exploited in ongoing or future smishing campaigns.”
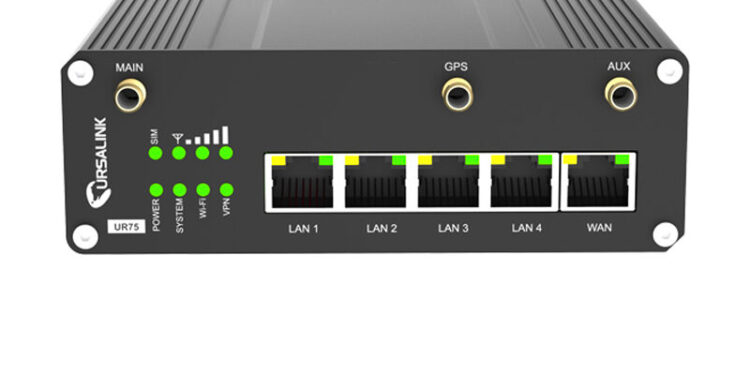
Sekoia mentioned it’s unclear how the gadgets are being compromised. One risk is thru CVE-2023-43261, a vulnerability within the routers that was mounted in 2023 with the discharge of model 35.3.0.7 of the gadget firmware. The overwhelming majority of 572 recognized as unsecured ran variations 32 or earlier.
CVE-2023-43261 stemmed from a misconfiguration that made recordsdata in a router’s storage publicly out there via an online interface, in accordance with a submit revealed by Bipin Jitiya, the researcher who found the vulnerability. Amongst different issues, a number of the recordsdata contained cryptographically protected passwords for accounts, together with the gadget administrator. Whereas the password was encrypted, the file additionally included the key encryption key used and an IV (initialization vector), permitting an attacker to acquire the plaintext password after which acquire full administrative entry.
The researchers mentioned that this principle was contradicted by a number of the details uncovered of their investigation. For one, an authentication cookie discovered on one of many hacked routers used within the marketing campaign “couldn’t be decrypted utilizing the important thing and IV described within the article,” the researchers wrote, with out elaborating additional. Additional, a number of the routers abused within the campaigns ran firmware variations that weren’t prone to CVE-2023-43261.
Milesight did not reply to a message looking for remark.
The phishing web sites ran JavaScript that prevented pages from delivering malicious content material except it was accessed from a cell gadget. One website additionally ran JavaScript to disable right-click actions and browser debugging instruments. Each strikes had been possible made in an try and hinder evaluation and reverse engineering. Sekoia additionally discovered that a number of the websites logged customer interactions via a Telegram bot referred to as GroozaBot. The bot is thought to be operated by an actor named “Gro_oza,” who seems to talk each Arabic and French.
Given the prevalence and big quantity of smishing messages, individuals typically marvel how scammers handle to ship billions of messages per 30 days with out getting caught or shut down. Sekoia’s investigation means that in lots of circumstances, the sources come from small, often-overlooked bins tucked away in janitorial closets in industrial settings.



![Joyful Gilmore 2 Director Defends Virginia’s Surprising Demise Scene [Exclusive]](https://www.vegasvalleynews.com/wp-content/uploads/2025/07/l-intro-1753470007-120x86.jpg)


